Identity theft, how not to be locked out of your digital life
The loss of an Apple, Google or Microsoft account can trigger a digital paralysis that blocks work and documents. Password managers, passkeys, trusted contacts, official apps and physical keys are the key tools to prevent the worst and make one's online identity recoverable.
We can no longer log into our Apple, Microsoft or Google account? This can be the beginning of a digital catastrophe. Sometimes password recovery fails, for many reasons. Suddenly we can no longer read mail, access our calendar, sign documents, open files in the cloud. For a professional or a company, this means blocked hours of work. Days, even.
So what to do? There are a few precautions to prevent the worst.
Password manager
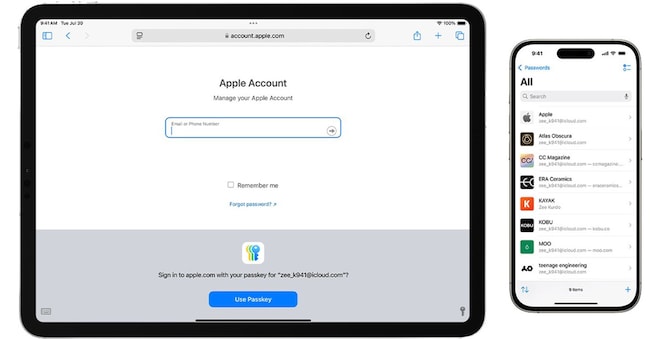
The first defence is a structured credential management. In practice, a password manager. An integrated one may be OK (Apple Passwords on iPhone, iPad and Mac; Google Password Manager in Chrome and Android; the integrated manager in Edge for Microsoft accounts), but for those working on mixed ecosystems, a stand-alone solution is often more effective.
Products such as Bitwarden, 1Password and Dashlane offer apps for all major platforms, browser extensions and additional functions such as breach control, secure credential sharing and passkey management. Dashlane and 1Password are often chosen by companies and professional firms for their combination of simple interfaces and administrative tools; Bitwarden, which is open source, is popular among advanced users and small businesses also thanks to a free plan that allows unlimited use on multiple devices.
First step: define a single long, complex but memorable 'master password'. Second: activate two-factor protection on access to the manager itself, using an authentication app or a physical key. Third: make sure the vault is synchronised in the cloud, so it can be opened from another device if the master is lost or stolen.