The shadow of hacker attacks and bot fraud on the World Cup
The threat is aimed at It infrastructures and ticket platforms. The solutions: predictive approach with AI and awareness
From domains aimed at fraud to bots for purchasing tickets to attacks on IT infrastructures: the range of threats hovering over the Fifa World Cup 2026 is vast and hints at the importance of a game that is played far away from the pitch, that of digital security. Several factors, starting with the size of the audience, make the tournament an attractive target for cybercrime and complexly structured malicious campaigns.
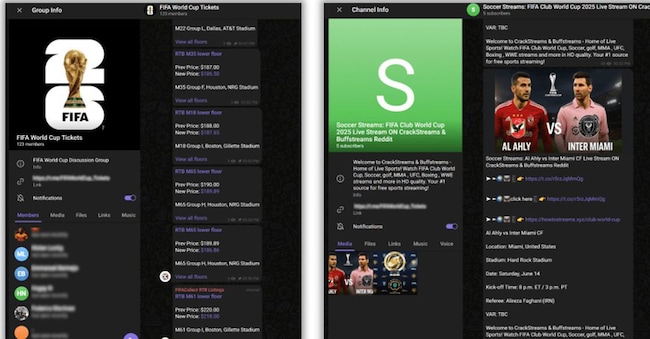
The list of identified threats includes a bit of everything, and the alert is at its highest, especially with regard to DDos attacks aimed at blocking broadcasts and phishing actions aimed at fans. That security is one of the facets of this major digital event is also indicated by the thousands of World Cup-related domains registered in the past months, often in an automated manner, to sell non-existent tickets, activate malicious streaming platforms or manage e-commerce of counterfeit merchandise.
An organic plan of offence
Not isolated initiatives, therefore, but an organic plan of offence involving the use of a few specific registrars, recurring language patterns and shared Dns infrastructures. All topped off with cross-channel 'promotion' of these fraudulent sites through social campaigns and sponsored ads on Telegram and the dark web. Kaspersky and Check Point experts have identified different types of scams that imitate official event sources (even replicating their official colours) or exploit their popularity for malicious purposes. A further attack scenario involves fraudulent e-mail campaigns, through which attackers try to induce users to send money or click on a phishing link; in some cases, the scam message contains a false claim to win $500,000 worth of tickets, flights and accommodation, followed by instructions to contact the sender to claim the 'prize'.
Ticketing platforms at risk
If fan scams are one side of the problem, the other reflects more sophisticated threats to active IT systems operating behind the scenes of the event, e.g. official ticketing platforms, which have already been targeted by botnets designed to saturate virtual queues and acquire large volumes of tickets. On the infrastructural front, the massive use of streaming services and mobile apps to ensure real-time coverage of the entire event inexorably widens the attack surface and also exposes security and logistics coordination systems to breaches. The distributed model of the tournament, spread across three nations and 16 different cities, also makes the protection perimeter more fragmented, with each node of the system (airports, hotels, stadiums, commercial facilities) becoming a potential point of vulnerability. There is therefore a second level of concern that involves the brands associated with the Fifa World Cup: a recent ProofPoint analysis shows that more than a third (36 per cent to be precise) of the World Cup 2026 partners, sponsors and suppliers do not have advanced security configurations in place to actively block spoofing email attempts.
Which means, for those on the hunt for tickets and promotional offers, direct exposure to apparently legitimate and trustworthy e-mail communications that are instead fraudulent. The underlying problem, as observed by the experts of the Californian cybersecurity company, is the incomplete adoption of the Dmarc (Domain-based Message Authentication, Reporting and Conformance) protocol, today considered the first line of defence against fraud perpetuated via e-mail: only a portion of the organisations analysed use the most restrictive modality, capable of preventing the delivery of unauthorised messages.