Microsoft is pulling the plug on Windows 10. Here's what you need to know
Microsoft's support for the Windows 10 operating system ended on 14 October.
Microsoft's support for the Windows 10 operating system ended on 14 October. This means that after that date, technical support, feature and security updates are no longer provided. There are three possible solutions and if not pursued, they open the door to possible IT security and privacy risks. Doing nothing is the only wrong choice.
Self-Assessment for Informed Decisions
In the case of the end of life of an operating system, digital adversaries immediately carry out passive web analyses (scans) to check for the existence of systems exposed to outdated vulnerabilities, with the aim of exploiting them: they try to take advantage of the case in which some organisation has not prepared in time.
Every organisation adopting the old operating system, if it has not already done so, should carry out a re-evaluation of the risks with respect to the number of devices affected, the type of data managed, and the possibility of adopting one of the solutions, especially in relation to the costs to be faced in relation to the cost of potential damage. But the risks may concern both the compatibility of updates with legacy business software and user downtime, which causes loss of productivity. Whatever the business condition, there is no one-size-fits-all choice. Each entity must self-assess in order to proceed consciously and appropriately.
The three solutions
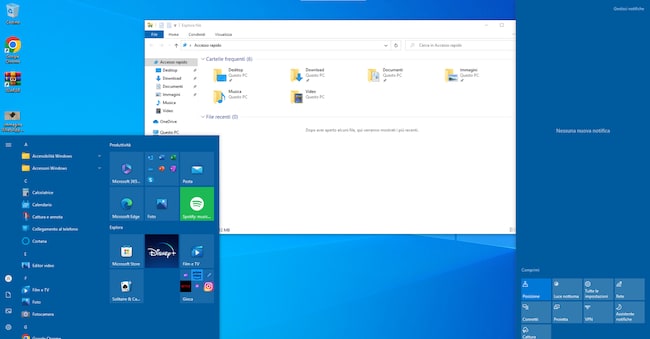
The recommendations coming directly from the parent company concern three possible choices: upgrade to the next version of the Windows 11 operating system on one's own device, if only the device is suitable to support such a step (and one can check in the 'check for updates' section if the automatic notification has not arrived); purchase a new device already equipped with Windows 11 in case the old device is not suitable for the new system; join the Extended Security Update (ESU) programme through paid membership to get support for one year (until 14 October 2026), gaining time to decide on hardware upgrades or replacements.
Potential risks
Users still using Windows 10 account for almost 60 per cent of companies, with 53 per cent of home users and even 8.5 per cent still using the obsolete Windows 7, whose support from Microsoft ends in 2020 (Source: Kaspersky Study). The greatest risk of not choosing a solution exposes one to significant security and privacy risks, as such operating systems become more vulnerable to digital attacks and can also become incompatible with installed and installable software and their security updates.